TeamViewer Security Breached by ZLoader Malware
Today’s attacks are becoming more sophisticated and can be tough to recognize and mitigate.
Organizations’ top priority remains to shore up internal security controls and perimeter defenses to mitigate threats. Using the latest robust application in malware protection should get the job done, but what about external threats you can’t recognize?
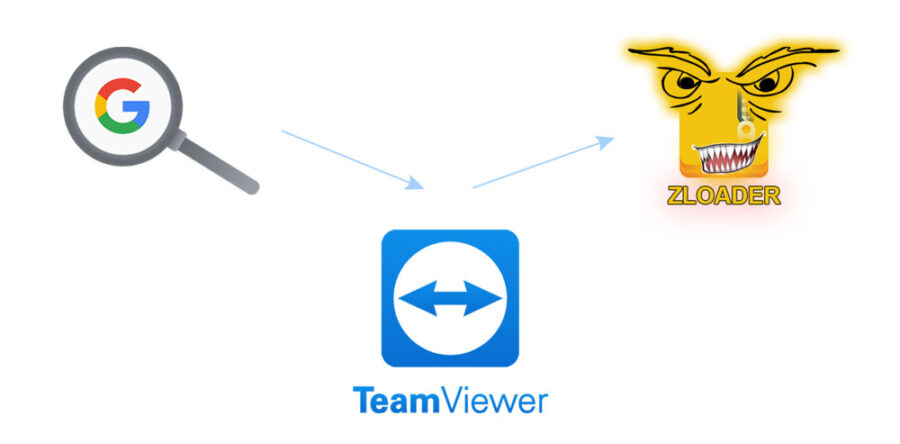
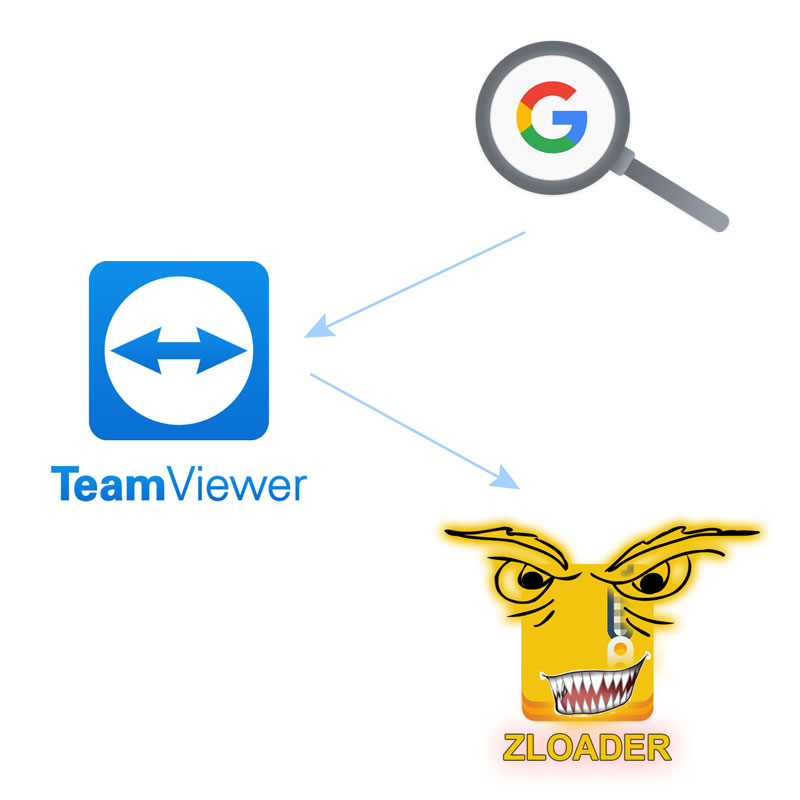
Recently bad actors used ZLoader (a malicious program designed to hijack Windows processes and the web browsers ) in a campaign initiated from Google search, fake TeamViewer ads placed on Google AdWords. This Malware disabled all Microsoft Windows Defender security software modules, according to SentinelOne research.
Zloader (dubbed DEloader by Fortinet) is a malicious program designed to hijack Windows processes and web browsers to steal sensitive information from users' machines. This malware uses stealth and evasion to backdoor into a version of the Windows utility wextract.exe to embed a payload and lower the chance of detection.
Imagine having endpoint protection software disabled by a user unaware of accessing a fake website with a clone of TeamViewer’s start screen. Google has become proficient in recognizing and protecting users from malware websites, but do you think that Google can distinguish and protect users from a Zloader downloaded file with malware inside?
SimpleHelp, a mature feature-rich alternative to TeamViewer provides secure remote-control capacities from a private or cloud-hosted system fully under your control. SimpleHelp also provides system monitoring and alerting, software and script delivery, as well as remote lab and remote work features.